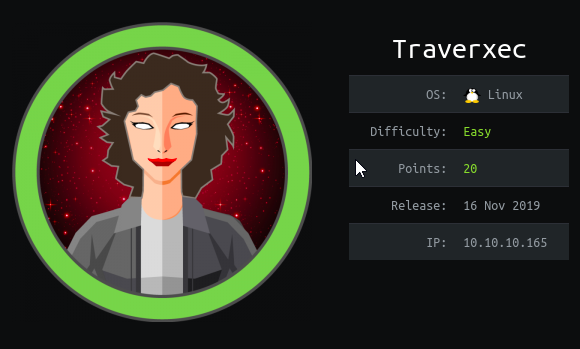
Hello all! This is Shreya Pohekar. Today we’ll be doing traverxec from hack the box. This box recently retired and is available for free in the retired machines section. So if you got stuck somewhere while the machine was active, follow the walkthrough and submit the flags.
The machine is an easy Linux box that requires you to do a bit of enumeration to find out the creds of admin. The initial foothold on the box is based on exploiting the Nostromo 1.9.6. But still getting to user was a bit tricky. Just need to study the right file. Privilege escalation to root was pretty simple as it exploited journalctl running with sudo.
With all that said, lets get started!!
Perform a nmap scan to find the open ports
# nmap -sC -sV -oA traverex.nmap 10.10.10.165
The nmap scan defines that notromo 1.9.6 is running on http. So we can search if the version is exploitable.
# searchsploit nostromo 1.9.6
Fire up http://10.10.10.165 in the browser and a website loads with portfolio theme
After reading the exploit, I got to know that the script takes 3 arguments
- IP
- Port
- Reverse shell
So I built up the query and set up a nc listener. Upon execution, I got the www-data shell
But access to /home/david was denied.
Upon enumeration, I found the the nostromo config file
I took the hash to hash identifier and the hash was identified as md5
The password cracked to be Nowonly4me, but there was unsuccessful ssh login or su david
So I reverted back to the conf file I was looking at and found something interesting. There is a directory public_www, accessible by the current user.
After traversing through the directories, I found the ssh backup file that had read permission.
So i transferred the file to my local machine using nc
After extracting the .txz, we got the .ssh files of the user david
I tried to ssh to david, but the id_rsa was encrypted with a passphrase. So now the id_rsa passphrase will be cracked using ssh2john
Now with the obtained password, login in with david user as follows and grep the user.txt
After getting the user level access, I found a bin directory present. I listed its contents using cat
Journalctl service was running with sudo privileges so I can edit the server-stats.sh to get to root.
In either way, just copy the last command uptil the pipe and type !/bin/bash . This can be used to access the files system with elevated privileges. In a nutshell, we are now root.
Thats all for the blog post. Thanks for reading.
Unitl then, Happy Hacking!!